
An easy cure to ransomware that people forgot about
 One of the police departments that was hit with ransomware in Massachusetts didn’t pay the ransom, yet were able to get their files unlocked. How did they do this, when even computer experts acknowledge the encryption is nearly unbreakable?
One of the police departments that was hit with ransomware in Massachusetts didn’t pay the ransom, yet were able to get their files unlocked. How did they do this, when even computer experts acknowledge the encryption is nearly unbreakable?
What they turned to was something quite basic. They had a long-standing policy of nightly backups of all police data. They also had a savvy IT manager – the minute he realized users were being infected he alerted all the users so additional files didn’t get encrypted. He then turned to the handful of users with encrypted files – and restored their mailboxes to last evening’s backup.
[clickToTweet tweet=" A smart IT organization didn’t pay a ransom yet got themselves running again – how did they do it?" quote=" A smart IT organization didn’t pay a ransom yet got themselves running again – how did they do it?"]
Yes, these users lost part of a day’s worth of files – but they quickly minimized the damage and avoided spending thousands in ransom dollars that the department didn’t have. While the ransomware incident was a sobering reminder of how quickly cybercrime can impact anyone, they relied on a fairly basic technology – backup – to fight off the attack.
While backup is one way to recover from a cyberattack, there are other ways to prevent them from occurring. In future blogs, we’ll look at those protections.
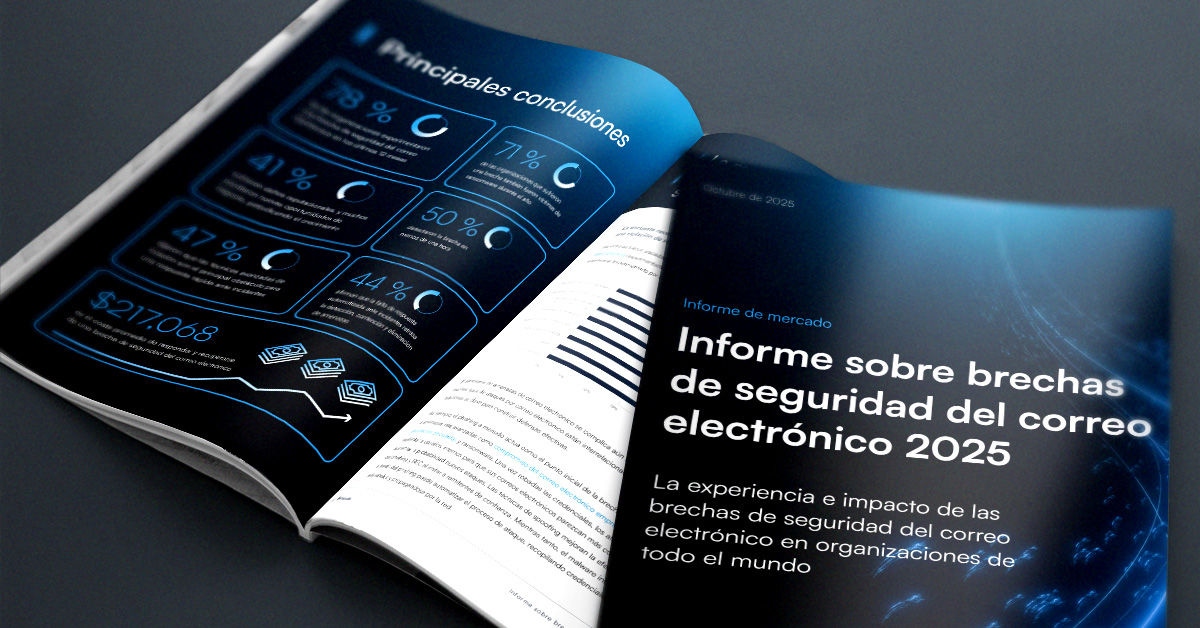
Informe sobre brechas de seguridad del correo electrónico 2025
Principales hallazgos sobre la experiencia y el impacto de las brechas de seguridad del correo electrónico en organizaciones de todo el mundo
Suscríbase al blog de Barracuda.
Regístrese para recibir Threat Spotlight, comentarios de la industria y más.
Informe sobre perspectivas de clientes MSP 2025
Una perspectiva global sobre lo que las organizaciones necesitan y desean de sus proveedores de servicios gestionados de ciberseguridad.





